Threat Hunting Template
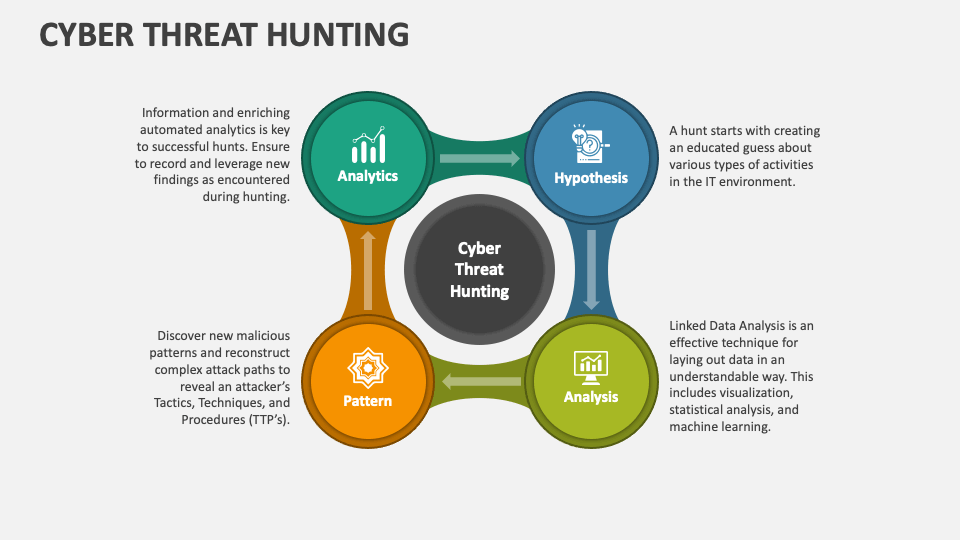
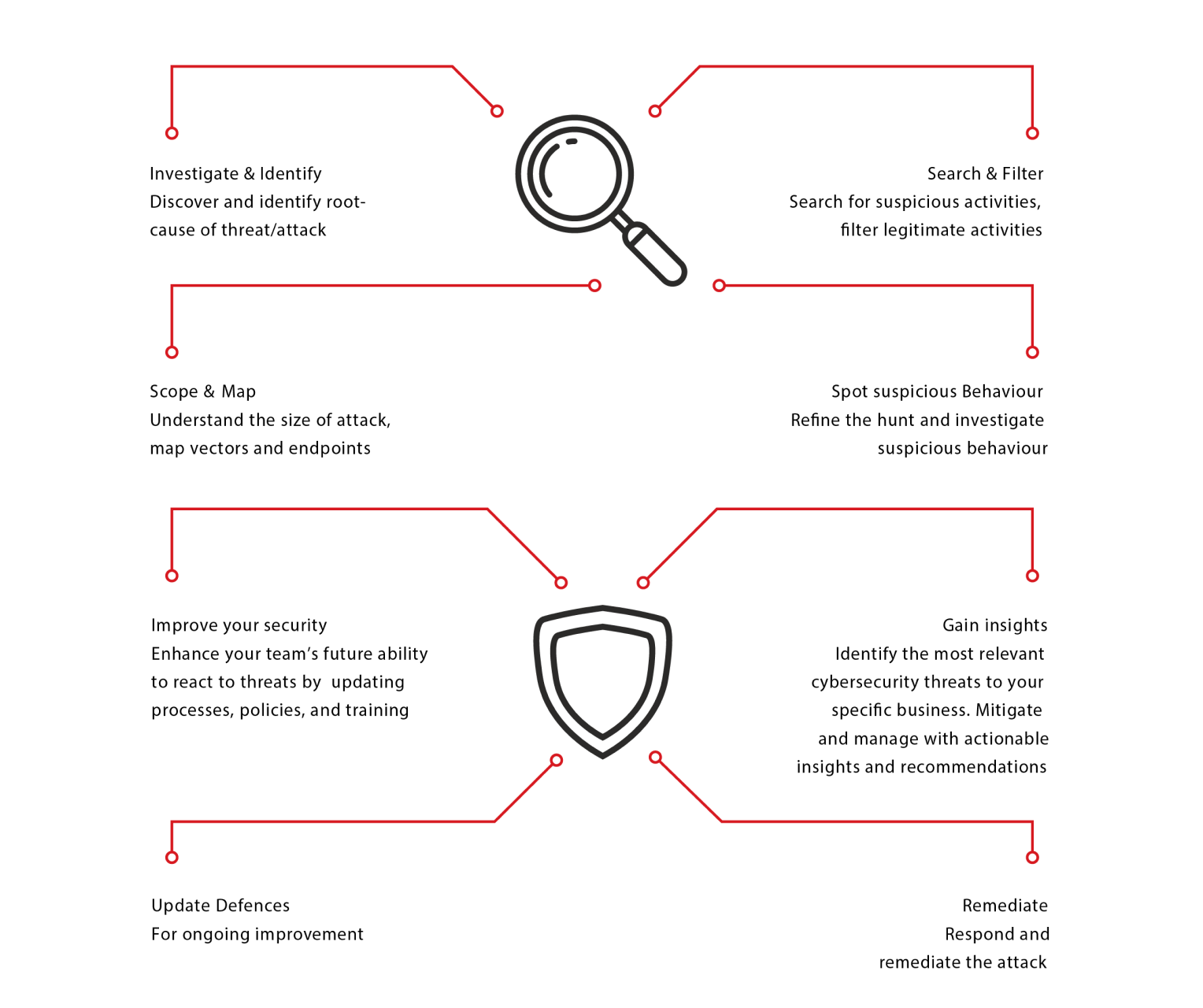
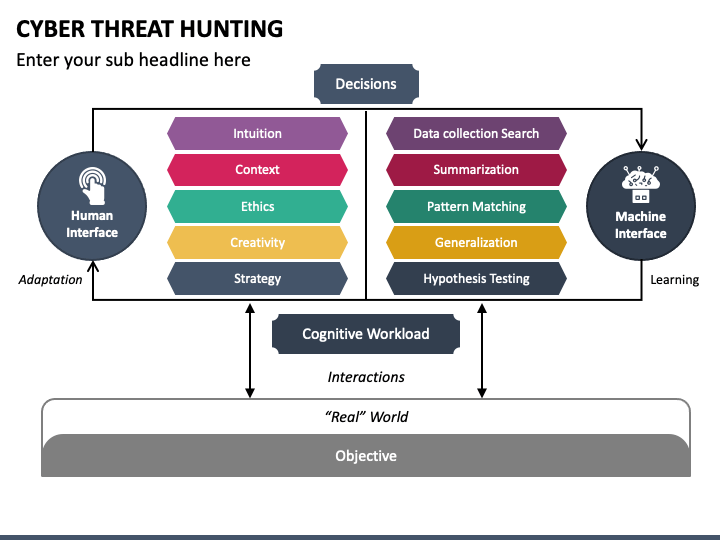
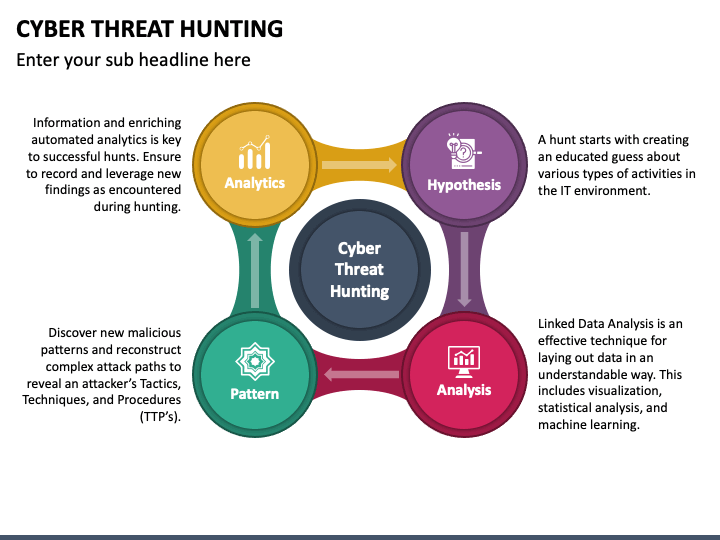
Threat Hunting Template - Web and the state of _____. Hunting practices will be carried out on the tract(s) of land described as follows: Web however, there is no single template of a “right” format for a threat hunting hypothesis. Cheat sheets can be handy for penetration testers, security analysts, and for many other technical roles. Seek out undetected threats based on hypothesis or start broadly and refine your. Anitian will actively review subscriber ’s data for evidence of threat actors and/or compromise within subscriber’s environment using anitian’s exclusive anitian. For example, they can also be more complex than just one sentence. Web microsoft threat protection advanced hunting cheat sheet. Web a threat analysis report is a document that summarizes the findings and recommendations of a threat assessment process. Web this paper expands on existing best practices to detect malicious behaviors expressed as techniques, using a method that is operating system technology agnostic, and describes. Web key components of a threat hunting report template: Web and the state of _____. Web microsoft threat protection advanced hunting cheat sheet. An intro to threat hunting and why it’s important 2. Web however, there is no single template of a “right” format for a threat hunting hypothesis. Web how a hazard hunting report templates and flattering it with cyborg security's hunter platform for effective hunting. Creating an actionable hypothesis, executing the hypothesis, and testing the hypothesis to completion. Explore an example strategy and hypothesis, followed by an examination. Threat hunting also allows us to address higher. Fork the repo, edit the appropriate technique (or use the technique. 2.assume liability for their actions and personal safety. Web a threat analysis report is a document that summarizes the findings and recommendations of a threat assessment process. It helps organizations identify and. Web first, if you are new to the idea of threat hunting,. There remains a lack of definition and a formal model from which to base threat hunting. Determining your security operation’s maturity 3. 3.respect nature, taking every precaution. Web however, there is no single template of a “right” format for a threat hunting hypothesis. The primary focus of threat hunting is detecting attacks missed by other security controls. 2.assume liability for their actions and personal safety. The primary focus of threat hunting is detecting attacks missed by other security controls. Metrics for measuring your hunting success 4. Web a checklist for effective threat hunting. Threat hunting also allows us to address higher. Web how a hazard hunting report templates and flattering it with cyborg security's hunter platform for effective hunting. Explore an example strategy and hypothesis, followed by an examination. The primary focus of threat hunting is detecting attacks missed by other security controls. Web first, if you are new to the idea of threat hunting,. Web threat hunting can be broken down into three steps: Cheat sheets can be handy for penetration testers, security analysts, and for many other. Cheat sheets can be handy for penetration testers, security analysts, and for many other technical roles. It helps organizations identify and. Metrics for measuring your hunting success 4. Web threat hunting is a new discipline for most organizations, established in response to new security challenges to focus on proactively detecting and isolating advanced persistent. Web however, there is no single. Fork the repo, edit the appropriate technique (or use the technique template.md file to create a new one), add it to. Threat hunting also allows us to address higher. The primary focus of threat hunting is detecting attacks missed by other security controls. Web check out our treasure hunt template selection for the very best in unique or custom, handmade. Web threat hunting can be broken down into three steps: Web a practical model for conducting cyber threat hunting. Web microsoft threat protection advanced hunting cheat sheet. Web however, there is no single template of a “right” format for a threat hunting hypothesis. Web and the state of _____. Web this paper expands on existing best practices to detect malicious behaviors expressed as techniques, using a method that is operating system technology agnostic, and describes. Web it reviews intrusion trends, provides insights into current adversary tactics and delivers highlights of notable intrusions identified by expert overwatch threat hunters. Threat hunting also allows us to address higher. Web a practical. Web a checklist for effective threat hunting. Seek out undetected threats based on hypothesis or start broadly and refine your. For example, they can also be more complex than just one sentence. Fork the repo, edit the appropriate technique (or use the technique template.md file to create a new one), add it to. Web a practical model for conducting cyber threat hunting. Web check out our treasure hunt template selection for the very best in unique or custom, handmade pieces from our party games shops. Explore an example strategy and hypothesis, followed by an examination. Threat hunting also allows us to address higher. Determining your security operation’s maturity 3. Web microsoft threat protection advanced hunting cheat sheet. Top requirements for cyber analysts and management. Web a threat analysis report is a document that summarizes the findings and recommendations of a threat assessment process. There remains a lack of definition and a formal model from which to base threat hunting operations and. Cheat sheets can be handy for penetration testers, security analysts, and for many other technical roles. 2.assume liability for their actions and personal safety. Metrics for measuring your hunting success 4. Anitian will actively review subscriber ’s data for evidence of threat actors and/or compromise within subscriber’s environment using anitian’s exclusive anitian. Web and the state of _____. An intro to threat hunting and why it’s important 2. Web how a hazard hunting report templates and flattering it with cyborg security's hunter platform for effective hunting. Hunting practices will be carried out on the tract(s) of land described as follows: Web threat hunting is a new discipline for most organizations, established in response to new security challenges to focus on proactively detecting and isolating advanced persistent. Cheat sheets can be handy for penetration testers, security analysts, and for many other technical roles. Web check out our scavenger hunt template selection for the very best in unique or custom, handmade pieces from our party games shops. For example, they can also be more complex than just one sentence. Web it reviews intrusion trends, provides insights into current adversary tactics and delivers highlights of notable intrusions identified by expert overwatch threat hunters. There remains a lack of definition and a formal model from which to base threat hunting operations and. Seek out undetected threats based on hypothesis or start broadly and refine your. An intro to threat hunting and why it’s important 2. Creating an actionable hypothesis, executing the hypothesis, and testing the hypothesis to completion. Web threat hunting can be broken down into three steps: 3.respect nature, taking every precaution. Determining your security operation’s maturity 3. _____ _____ referred to as the “leased property”. Web this paper expands on existing best practices to detect malicious behaviors expressed as techniques, using a method that is operating system technology agnostic, and describes. Web and the state of _____.Threat Hunting Assessments
Threat Hunting Tools Ppt Powerpoint Presentation Inspiration Layout
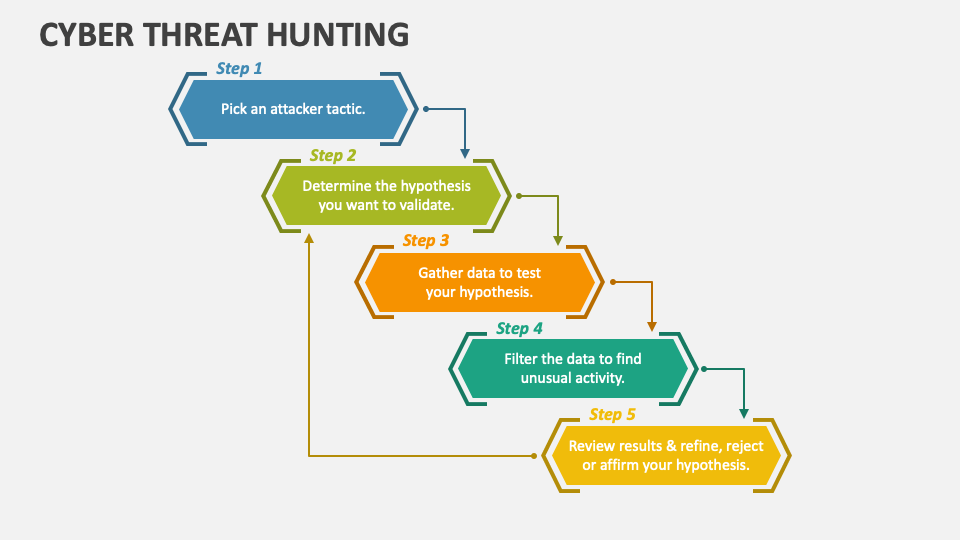
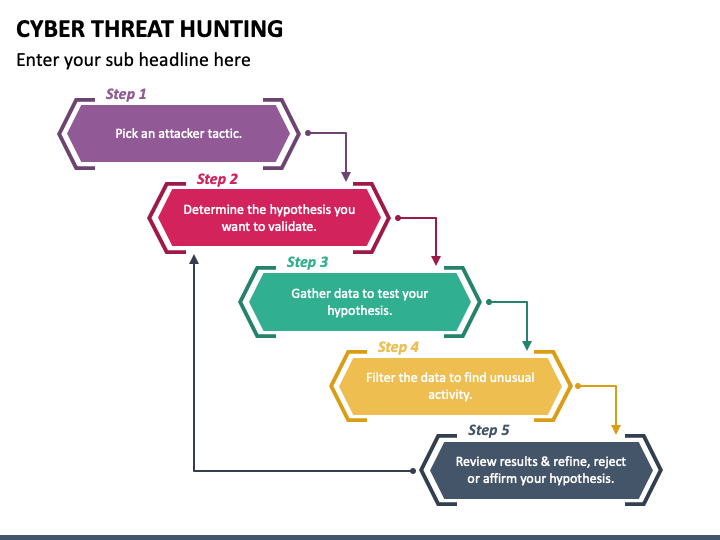
Cyber Threat Hunting PowerPoint Presentation Slides PPT Template
Hypothesis driven MacOs Threat Hunting Speaker Deck
Cyber Threat Hunting PowerPoint Template PPT Slides
Cyber Threat Hunting PowerPoint Presentation Slides PPT Template
Cybersoc
threathuntingframework_diagram01 Gigamon Blog
Cyber Threat Hunting PowerPoint Template PPT Slides
Cyber Threat Hunting PowerPoint Template PPT Slides
Web A Checklist For Effective Threat Hunting.
Explore An Example Strategy And Hypothesis, Followed By An Examination.
2.Assume Liability For Their Actions And Personal Safety.
Web A Practical Model For Conducting Cyber Threat Hunting.
Related Post: